Our news
-
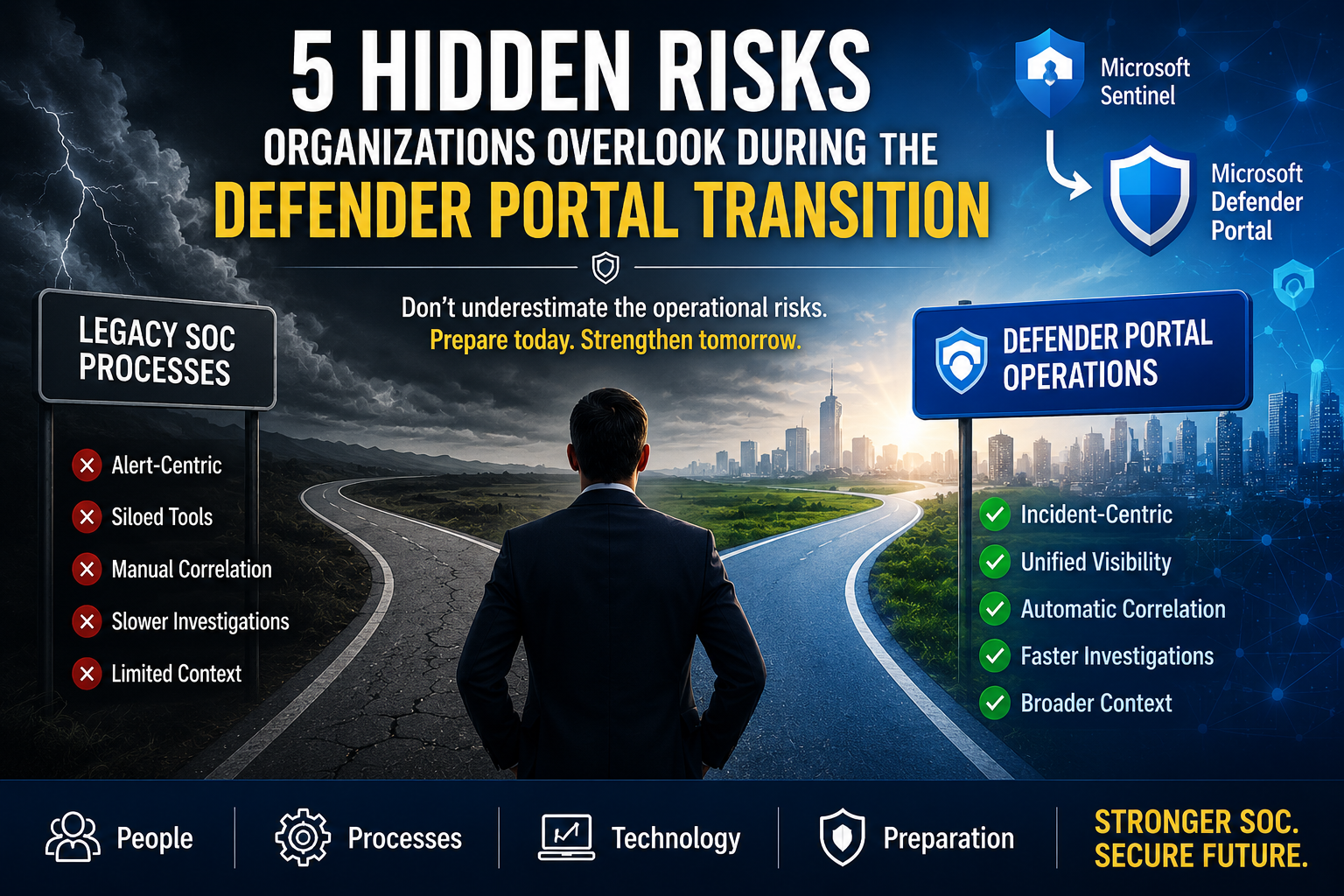
5 Defender Portal Risks Security Leaders Overlook
The Defender Portal Transition introduces more than a new interface. Discover five hidden risks that can impact analyst workflows, automation, training, and security operations—and learn how to prepare your SOC for success.
-

Critical Sentinel Shift Security Leaders Can’t Ignore
Microsoft Sentinel’s transition into the Microsoft Defender portal is far more than a simple UI update. This shift changes how SOC teams investigate incidents, correlate threats, and operate across SIEM and XDR workflows. Learn why security leaders should begin preparing now to reduce operational risk and modernize security operations effectively.
-

The Path to an Autonomous SOC: From Signals to Self-Driving Security Operations
The autonomous SOC is not a product you can deploy overnight. It is built through strong identity, signal-driven operations, detection engineering, data strategy, and AI working together. This post outlines the maturity journey and shows how organizations can move toward autonomous security operations with measurable outcomes.
-

Measuring Security Outcomes: What Actually Matters in a Modern SOC
Security metrics for SOC operations should measure outcomes, not activity. This post explains how to move beyond alerts and ticket counts to focus on MTTD, MTTR, and real-world effectiveness, using Microsoft Sentinel and Defender XDR to track meaningful security performance.
-

Where AI Actually Helps Security Teams (and Where It Doesn’t)
AI in security operations is often overhyped, yet its real value comes from strengthening investigation, triage, and signal correlation. This post breaks down where AI truly helps security teams, where it falls short, and how leaders can align it with data strategy, detection engineering, and Microsoft Sentinel to drive meaningful outcomes.
-

Designing a Data Strategy for Modern Security Monitoring
A strong data strategy for modern security monitoring determines whether a SOC produces clarity or noise. This post explores how security leaders should prioritize telemetry, manage ingestion costs, and align data sources with detection engineering and Microsoft Sentinel operations.
-
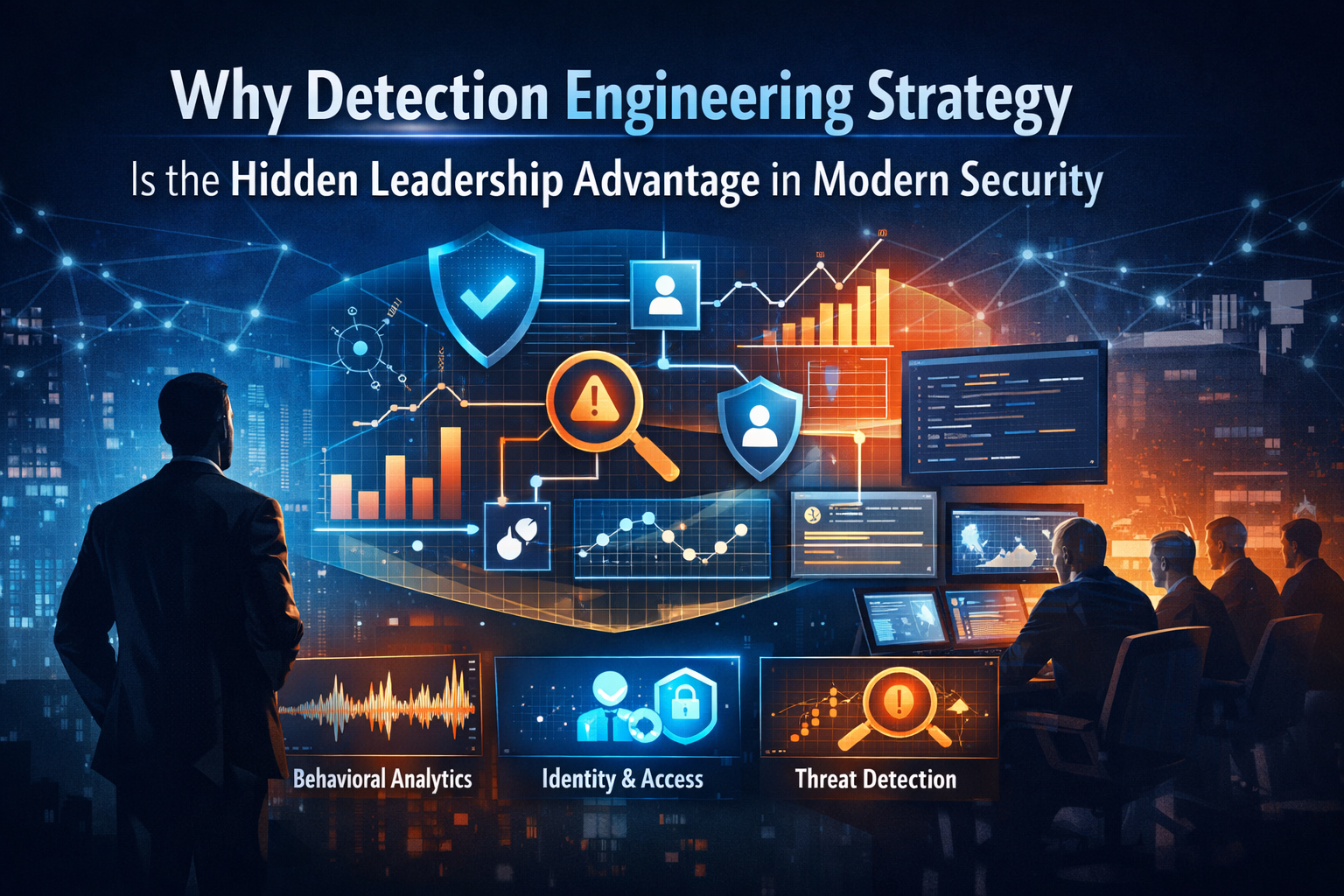
Why Detection Engineering Strategy Is the Hidden Leadership Advantage in Modern Security
Detection engineering strategy is more than analytics rule creation. This post explores why leaders shape detection quality, how identity and signal design influence outcomes, and why modern security success depends on strategic engineering, not alert volume.
-

Why Modern Security Must Move Beyond Alerts and look at Signals
Modern security operations can no longer scale around alerts alone. This post explores why signal-driven SOC operations are essential for reducing noise, improving investigations, and enabling effective monitoring with platforms like Microsoft Sentinel.
-

Identity Is the New Security Control Plane
Modern security no longer scales around networks or tools. This post explores how identity-centric security architecture reshapes trust, access decisions, and monitoring, and why this shift directly impacts security operations and platforms like Microsoft Sentinel.
-

A New Year Reset for Security Leaders: From Announcements to Architecture
As security enters a new year, leaders face a shift that goes beyond tools and announcements. This post explores what recent industry direction reveals about identity, architecture, and the future of modern security leadership.